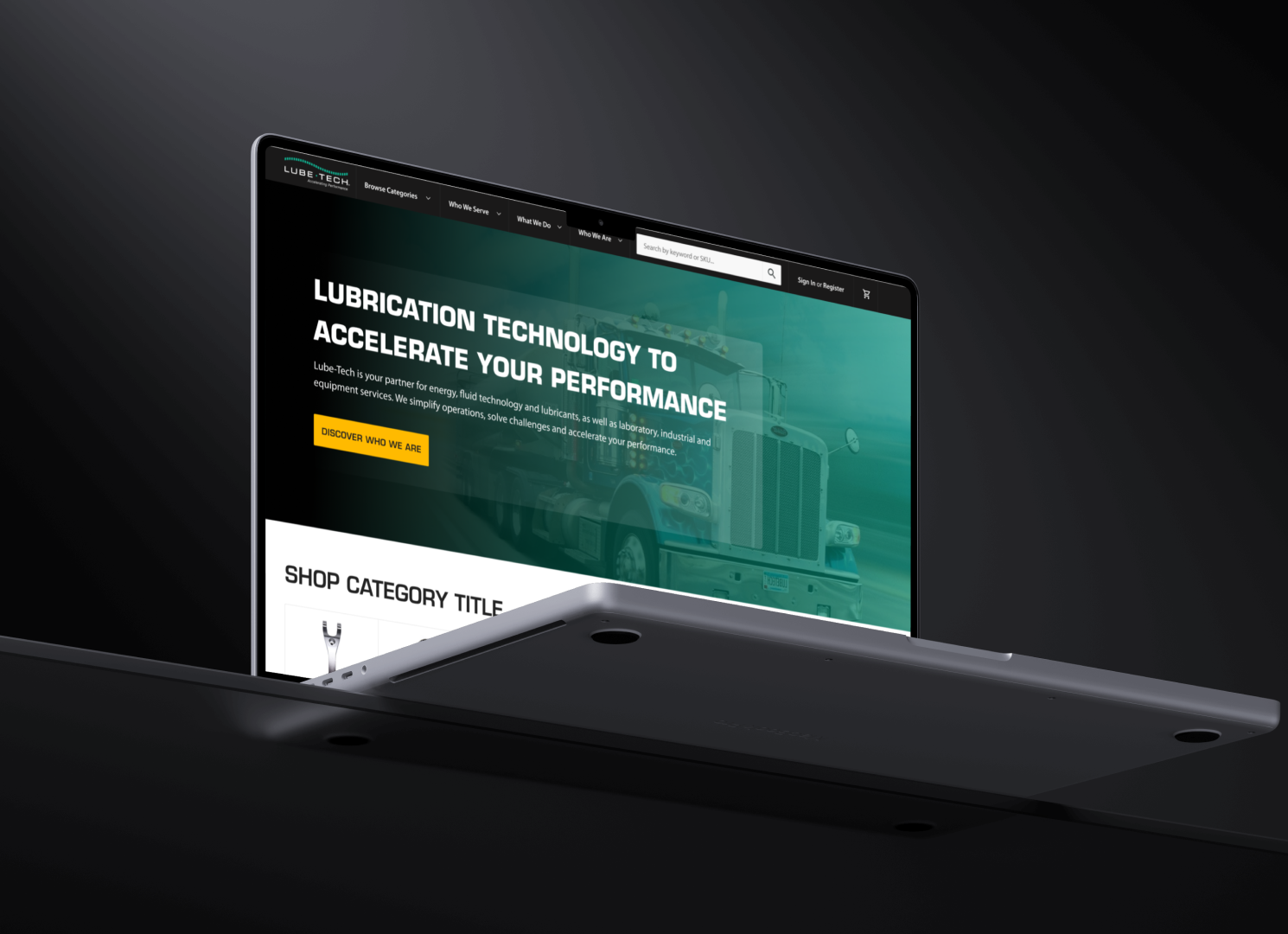
End-to-end strategy, design, & engineering for meaningful experiences
Successful businesses don’t just react; they transform. We help organizations identify opportunities, optimize operations, and implement solutions that drive measurable growth and long-term success.